Rummy Gold is a free-to-play card activity from developer Moonfrog. This allows you to Enjoy quite a few rummy card activity modes revolving round the Indian Rummy variant, arguably the most well-liked Edition from the classic card activity from the subcontinent.This sport is intended for an Grownup audience and isn't going to offer true revenue ga
The Fact About rewards rummy games with referral incentives That No One Is Suggesting
How would be the reward structured? Shoppers get a similar reward For each and every successful referral, with no limit to how many friends they're able to referWant far more? The next illustrations are referral headlines and slogans that you could customise and make your personal.Increase the advocate reward price: Rewards are meant to excite and
The smart Trick of rummy golds copyright That Nobody is Discussing
Protection commences with knowing how developers obtain and share your knowledge. Information privateness and protection methods may range depending on your use, region, and age. The developer furnished this details and may update it after some time.We’d like to focus on that every so often, we may perhaps overlook a possibly destructive software
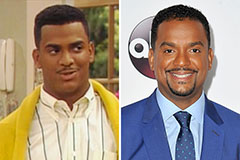 Alfonso Ribeiro Then & Now!
Alfonso Ribeiro Then & Now! Judd Nelson Then & Now!
Judd Nelson Then & Now! Michael Bower Then & Now!
Michael Bower Then & Now! Pauley Perrette Then & Now!
Pauley Perrette Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now!